As COVID-19 cases spike in the U.S., the FBI is warning about a new ransomware attack aimed at the U.S. Healthcare system. In an alert issued on Wednesday, the government said cybercriminals have launched an attack that has already impacted at least five U.S. hospitals and has the potential to impact hundreds more, according to the Associated Press.
Security experts believe the ransomware, known as Ryuk, which is one form of ransomware that The Cipher Brief reported on earlier this week, is believed to have originated in August of 2018 and is most likely the creation of a financially-motivated, Russian criminal organization known as Grim Spider.
The latest warning from the government follows a different kind of warning that the Treasury Department’s Office of Foreign Assets Control (OFAC) released earlier this month, reminding businesses that if they pay ransom to cyber hackers, they could be violating OFAC regulations and exposing themselves to government fines.
Earlier this week, we brought you The Ransomware Conundrum, which included a range of key expert perspective on what this could mean for businesses.
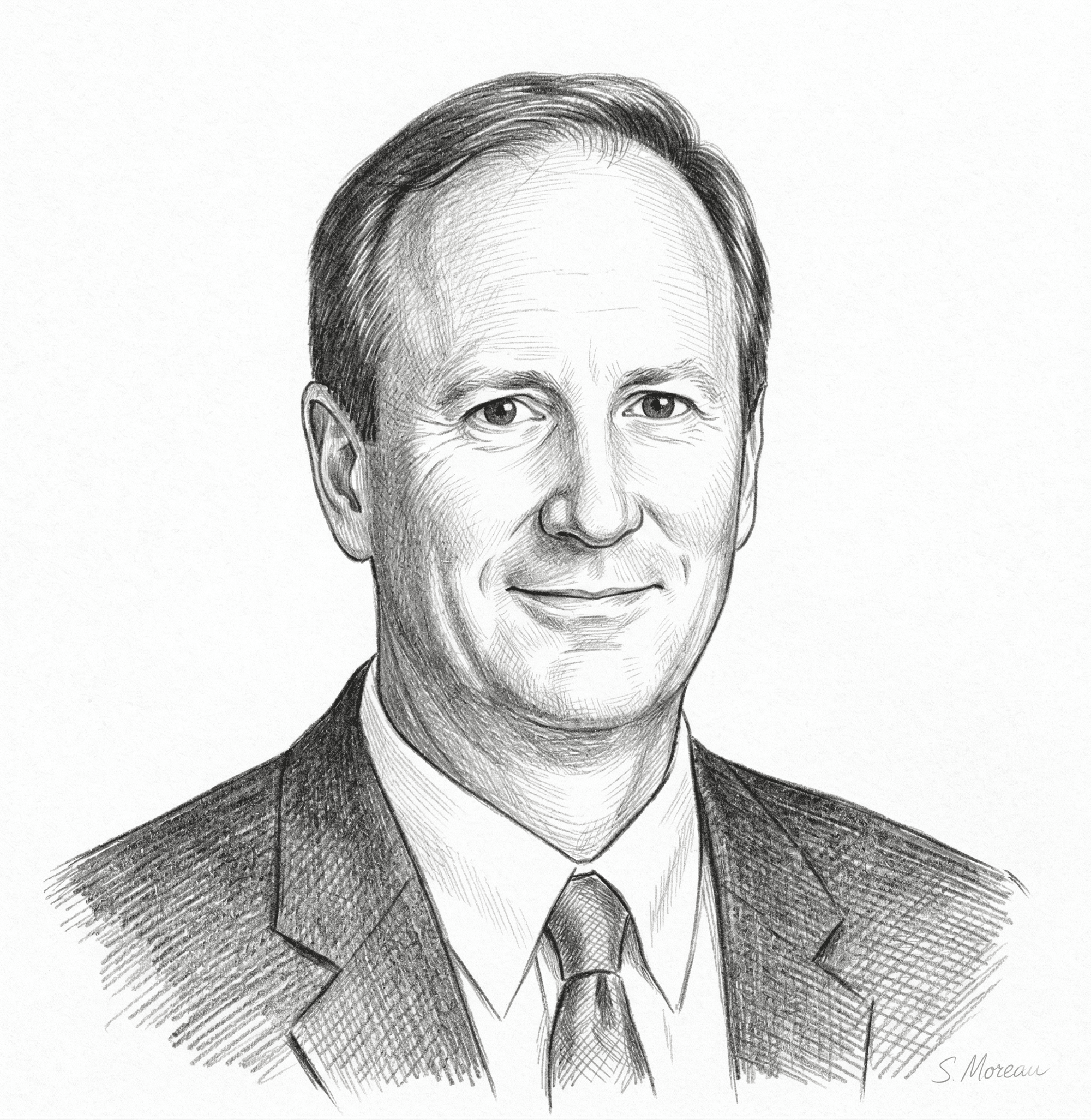
Cipher Brief Expert and former Assistant Attorney General for National Security John Carlin talked with us about what the latest advisory could mean and what businesses can do about it.
Carlin currently chairs Morrison & Foerster’s Global Risk and Crisis Management practice and is also the author of Dawn of the Code War: America’s Battle Against Russia, China and the Rising Global Cyber Threat.
The Cipher Brief: What is your biggest concern if the U.S. government decides to impose sanctions on companies that fall under the recently released OFAC advisory?
Carlin: It’s good that there was guidance put out there. There have been a lot of questions and confusion around this. Companies want to do the right thing and getting clarity on what steps they’re supposed to take is a positive.
In terms of enforcement, it’s a strict liability regime, but I hope the guidance is consistent with the goal to not re-victimize victims: If you follow the guidance and cooperate fully and openly with law enforcement early on in an investigation and seek to use a vendor to make a payment, the message seems to be that we’re not going to spend our time going after you, a victim who has followed the correct steps.
It remains to be seen if the government is signaling that if a company willfully makes a payment - or chooses not to avail itself to law enforcement and speaks with a reputable vendor who can do an OFAC check - if they might act. In other words, if you can’t show that you’ve taken the right steps before making a payment to a designated entity, the government may take action against your company.
The advisory is directed toward the industry that has sprung up to transact these negotiations and make payments- reminding them that they need to take these steps. I think the government would be more willing to go after those who are turning this into a for-profit business rather than going after the victims.
The Cipher Brief: You’re suggesting that the U.S. Government is looking to reinforce the rules for the third-party ransomware negotiator industry?
Carlin: Yes. And two additional areas that are in a similar vein and need more guidance would include banks and insurers. We have very little visibility on when these transactions occur. So, I think additional guidance, whether in the form of written policy or discussion is a needed next step.
The bigger picture, however, is that the problem of ransomware is not going to be solved by sanctions alone. We need to think through our policy on ransomware so that these attackers don’t end up going after the same victims twice.
The U.S. government works with like-minded partners throughout the world, because this isn’t just a U.S. issue- we all want to deter and disrupt the bad guys. If you’re going to forbid payments, you have to work on providing help on the front end with resilience for the companies, especially small and medium-sized companies.
The Cipher Brief: For those smaller companies, this issue can be more challenging and intimidating in terms of resources and capabilities. Are there additional things the federal government could be doing, such as providing better information sharing, to help support those smaller and mid-sized companies?
Carlin: There needs to be an improvement on information sharing. They could also provide free assessments for businesses and work to make sure that there isn’t increased liability for getting an assessment. We’ve already done that with physical site security.
We could also outsource solutions for smaller companies and incentivize the use of that solution. We can also encourage people to get insurance. These are all possible solutions that deserve additional thought.
The Cipher Brief: What advice would you have for those smaller and mid-sized companies and their boards on how to interpret the reminder that sanctions are a possibility if you don’t do things the right way?
Carlin: This applies to every size company and is still the exception more than the norm. Boards should ensure that there is a policy in place that lays out factors that determine if they should make a ransomware payment or not. This policy should include what is now laid out in OFAC and should be kept private.
And most importantly, boards and organizations should try to avoid having to make a payment by asking what their resilience plans are and making sure that they understand the answers.
Read also, Navigating the Ransomware Conundrum with Accenture Security's Kelly Bissell, and What the OFAC Advisory means for Companies that pay Ransom with former Assistant Secretary of the Treasury for Intelligence and Analysis, Leslie Ireland exclusively in The Cipher Brief.
Read more expert-driven national security insight, perspective and analysis in The Cipher Brief