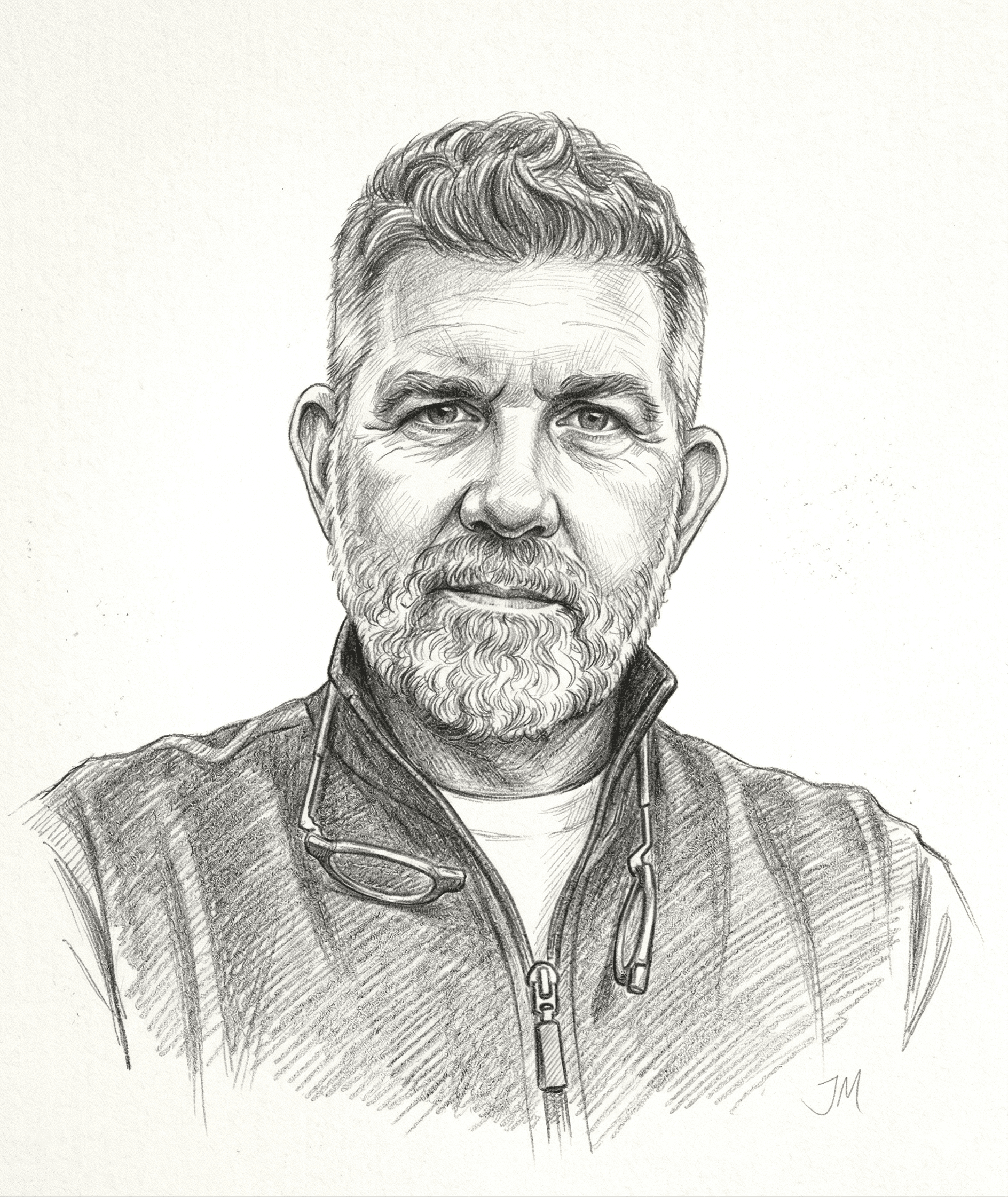
Walter Pincus is a contributing senior national security columnist for The Cipher Brief. He spent forty years at The Washington Post, writing on topics from nuclear weapons to politics.
OPINION — “Cyber is now the critical domain to every facet of our National Security.”
Those words were spoken last Friday by Rep. Mike Gallagher (R-Wisc.) at a hearing of the House Armed Services Subcommittee on Cyber, Innovative Technologies, and Information Systems, where, in the wake of the Colonial Pipelines hack, government witnesses described the increase in such attacks and House members called for more government funds, attention and responses to be devoted to deterring those activities.
Gallagher, ranking member of the subcommittee, is hardly a novice on the subject of cyberspace. He served as co-chair of the bipartisan Cyberspace Solarium Commission which in March 2020, came up with 25 recommendations which were later adopted into law. The subcommittee chairman, Rep. James Langevin (D-R.I.), is also a member of the Solarium Commission and together the two have taken an active interest in “Operations in Cyberspace and Building Cyber Capabilities Across the Department of Defense,” which was the title of Friday’s hearing.
Ms. Mieke Eoyang, Deputy Assistant Secretary of Defense for Cyber Policy, told the members, “The cyberspace domain is both more important and more contested that it has been in recent memory.”
She pointed out that because of “our growing reliance on technology, cyber criminals and major state actors alike took advantage of COVID-19 by releasing ransomware on health care facilities, targeting vaccine production and supply teams, exploiting fear by spreading disinformation and even disrupting pipeline companies.”
Describing the unique situation that has arisen, she said, “The line between nation state and criminal actors is increasingly blurry as nation states turn to criminal proxies as a tool of state power — and then turn a blind eye to cyber crimes perpetrated by the same malicious actors.” She described that technique as “a common practice for Russia, whose Security Services leverage criminals while shielding them from prosecution for crimes they commit for personal benefit. We have also seen some states allow their government actors to moonlight as cyber criminals.”
Gen. Paul M. Nakasone, Commander, U.S. Cyber Command and Director, National Security Agency (NSA), told the House panel that Russia in the Solar Winds attack, showed it could invade other companies using one company’s supply chain; and China, in the hack of Microsoft’s Exchange, showed one system’s vulnerabilities allowed attacks on other systems around the world. Nakasone added that the Colonial Pipeline attack illustrated “a growing trend of companies and even government agencies being held hostage by malicious actors.”
Nakasone also noted the increase in activity. “Over the past 14 months,” he said, “we’ve seen a tremendous difference in the [cyber] environment. Adversaries are demonstrating a changed risk calculation. They are undertaking malign activities in cyberspace at greater scope, scale and sophistication. They desire to take on the United States in cyberspace below the level of armed conflict.”
The Cipher Brief hosts private briefings with the world’s most experienced national and global security experts. Become a member today.
The subcommittee members brought up a wide range of subjects beginning with the possible establishment of a Digital Service Academy which, as Rep. Rogers (R-Ala.) said, “would help train a person to take on this [cyber] challenge.” Nakasone talked of Cyber Excepted Service, a 2016-created occupational structure for the Defense Department’s cyber community which provides greater flexibilities and options for recruiting and retaining cyber professionals. He said it has become “an avenue for us to be able go to recruiting fairs and offer final job opportunities and opportunities for young people to consider a career with Cyber Command.” He also said there has been a dramatic drop in the time it takes to get a security clearance if hired under Cyber Excepted Service. In the past, it took some 110 days to bring someone into the civilian service, while now it has dropped into the 60-day range, Nakasone said.
Rep. Elissa Slotkin (D-Mich.), a former CIA analyst and Pentagon official during the Obama administration, told Nakasone she thought it “would be really important to truly present a transformational budget on cyber whenever you guys submit it. I think the committee is crying out for it. I think the country is crying out for it, and we know that it will come at the expense of older systems, legacy systems [and] pork. And Congress has the responsibility to help you with that, which we don’t always live up to. But I really want to encourage you to be bold and provide something that really helps move us into the 21st Century so we can maintain our military edge.”
Slotkin also raised the issue of secrecy that surrounds the ways in which Cyber Command and NSA respond to publicized cyber attacks.
She said the American people “are on the front lines of the attack, yet they can’t feel, they don’t know what their country is doing to respond. I know that’s a difficult position for you all. What you do should be under the radar. But I would just note there is a real sense that there is no deterrent on a cyber attack – that a Russian group or a Chinese group can attack us with impunity.”
Slotkin ended by saying, “We are going to need to figure out how to not just do it in the shadows but communicate to the American people that we are not leaving ourselves open as this becomes the primary form of attack on the average American citizen.”
The secrecy surrounding Cyber Command’s or NSA’s responses to foreign attacks reminded me of that time during the Vietnam War, when the U.S.-directed bombing of North Vietnam supply routes in Laos was classified. I was then working for Sen. J.W. Fulbright (D-Ark.), chairman of the Senate Foreign Relations Committee. After personally observing U.S. forward air controllers in action in Laos, I participated in the Fulbright committee hearings on the bombing in Laos which eventually led the Nixon administration to publicly disclose what was going on. The Fulbright argument was that the Russians, Chinese, Laotians and North Vietnamese knew the U.S. was running the bombing, only the American public did not know.
The cyber response situation appears to be similar.
Gen. Nakasone, in his opening statement last Friday, said, “U.S. Cyber Command conducted more than two dozen operations to get ahead of foreign threats before they interfered with or influenced our elections in 2020. I am proud of the work the command and the election security group performed.” Later, while answering a question, he said that during 2020, his Cyber Mission Teams undertook 11 projects overseas in 9 countries as part of the U.S. election security effort.
It is time either Nakasone or the White House describes the details of those operations to give the American public the confidence that a real response has taken place that will the rise of cyberattacks. The Russians, Chinese and criminal hackers are aware of what the U.S. response has been. It’s time the American people know, too.
Read more expert-driven national security insights, perspective and analysis in The Cipher Brief