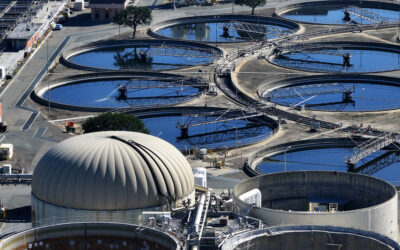
Assessing the Cyber Threat to the Nation’s Water Supply
BOTTOM LINE UP FRONT — It’s a serious threat to the nation’s critical infrastructure that not enough people are talking about. That’s the view of […] More
“Hey Thorne. Don’t get caught, my wife likes it here.” That was the Deputy Chief of Station’s regular advice to all case officers prior to their agent meetings. The message was clear: identify threats to the operation, mitigate those risks, and fully understand the consequences for failure – arrest, detention, interrogation for the case officer and certain imprisonment; possible torture or death – for the source.
The removal of the DCOS and his wife following an operational failure by his subordinate was more than an inconvenience. It reduced the collection capabilities of the station and increased reputational risk for the larger organization. Few people, (informants and sources in espionage parlance and customers in the business vernacular), are likely to collaborate with an organization that cannot protect their most sensitive information. The components of classical espionage – obtaining privileged information, overcoming multiple levels of security, and protecting the source of the information – have useful lessons that extend to the rest of government, industry, and more specifically, the realm of cybersecurity. Cybersecurity and espionage share fundamental and unique characteristics – the protection of valuable information, identifying risks, communicating those risks to stake holders, and mitigating the risks to accomplish the mission.
Risk is an elastic term that takes on different meanings to different constituencies; military, intelligence, law enforcement, and business professionals each have their own risk vernacular. Even within the intelligence community, risk takes on different shades and hues: from the case officer who relies on humans for plans and intentions, the technical officer who places his or her confidence in the rigor and formulas of scientific systems, to the analyst who values all collection – but none too much. Risk criteria and risk parlance change within the IC based on what can be lost – human lives, complex and expensive systems, or the trust of policymakers.
The wars in Afghanistan, Iraq, and unnamed conflict zones has brought together professionals with diverse expertise in military operations, intelligence, and law enforcement towards a common goal. The participation in joint operations and combined task forces around the world has forged a common language through common experience. That same level of collaboration and cooperation found in the war zones can be applied to challenges of cybersecurity. Borrowing terminology from high threat occupations can establish a common lexicon of risk that is applicable to the private and public sector in this ever-evolving area of operation.
The world of human intelligence operations has a rich vocabulary of operational tradecraft – terms that describe the methods and techniques used to mitigate risk. Some of these terms have a cyber security corollary and provide a point of reflection for the daunting and complex task of information security in the cyber era. Here are a few to consider:
Collect: Survey your risk factors and know your risk status.
Consequences: What are the consequences of failure?
Mitigation: What actions can be taken to reduce risk?
Continuity: In the event of compromise, how do I continue the mission?
Communications: Do my team members, up and down the chain of command, understand the risks?
Cybersecurity is fluid and dynamic – the lexicon to explain it needs to adapt as well.
Related Articles
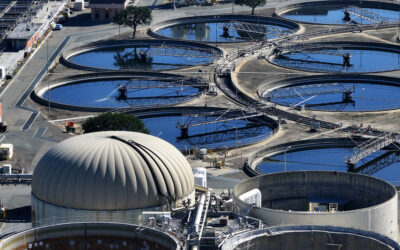
BOTTOM LINE UP FRONT — It’s a serious threat to the nation’s critical infrastructure that not enough people are talking about. That’s the view of […] More

SUBSCRIBER+ EXCLUSIVE REPORTING — Russia’s reaction to the new infusion of U.S. aid for Ukraine has ranged from shrugs to fury, from warnings of nuclear […] More

SUBSCRIBER+ EXCLUSIVE REPORTING — When Chinese President Xi Jinping came to San Francisco last November to meet with President Joe Biden, Chinese pro-democracy activists in […] More

SUBSCRIBER+EXCLUSIVE EXPERT PERSPECTIVE — More than two years after its withdrawal from Afghanistan, the U.S. still does not have a clear way forward in the […] More

SUBSCRIBER+ EXCLUSIVE REPORTING — Ukrainians greeted Saturday’s long-awaited House passage of $60.8 billion in aid with justifiable jubilation. For months, their soldiers, civilians, and political […] More

SUBSCRIBER+ EXCLUSIVE REPORTING — A race for control of space is underway, and just as on earth, the U.S. and China are the top competitors. […] More
Search