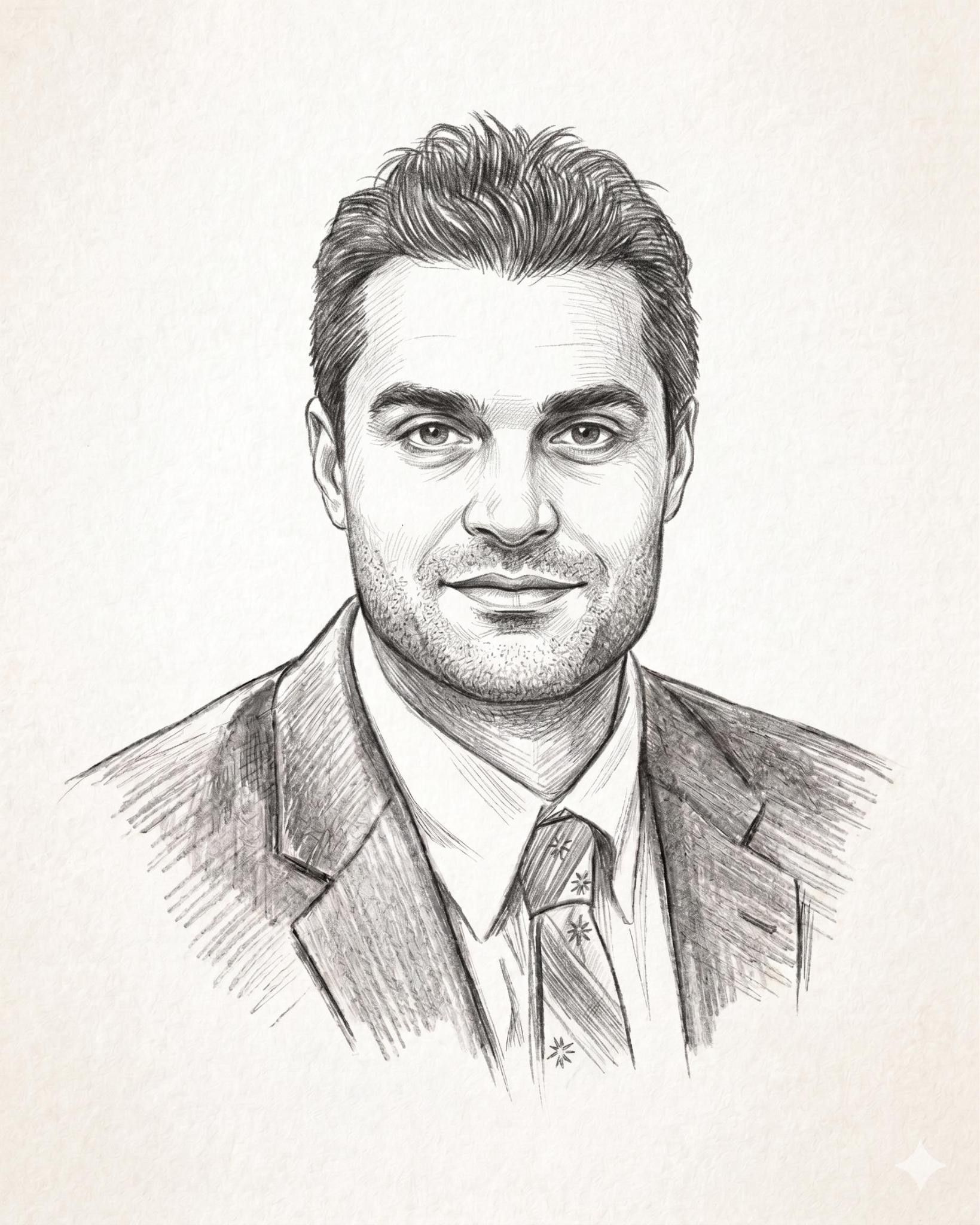
Cipher Brief Expert Daniel N. Hoffman is a retired clandestine services officer and former Chief of Station with the Central Intelligence Agency. His combined 30 years of government service included high-level overseas and domestic positions at the CIA. Hoff man is an advisor to Vaillance Group.
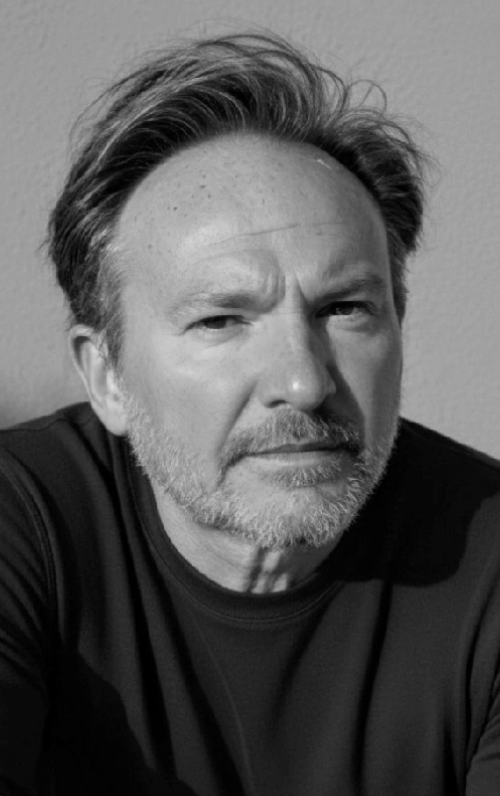
Shawnee Delaney was a clandestine officer and former Detachment Chief for the Defense Intelligence Agency and IT Specialist for the Department of Homeland Security for 10 years. She is a subject matter expert on insider threat and is the CEO of Vaillance Group.
OPINION — If there is one thing we have learned from doing business during the COVID-19 pandemic, it is the great benefits but also associated risks, of relying on cyberspace. A force multiplier for free expression and commerce, cyberspace is also an unregulated playing field subjected to exploitation from adversaries like China, Russia, Iran, and North Korea as well as criminals and terrorists.
Now more than ever, organizations are recognizing that no matter what technical controls and policies they have in place, it is the human threat (both internal and external) that is their greatest vulnerability. While use of the internet enables companies to get work done, it also leaves them and their employees vulnerable to exploitation.
The shift from working in an office, with security measures long in place, to a home environment has highlighted a new set of security risks to businesses including the use of personal unprotected devices, a general lack of cyber hygiene, and an ignorance of the vulnerabilities employees pose to their companies.
When we served in the U.S. Intelligence Community, being in the incident response phase - or “to the right of boom” – of a counterterrorism operation meant we had not collected enough of the disparate intelligence or perhaps did not analyze it properly in order to prevent an attack. In most cases, terrorists, like hackers, conduct reconnaissance before mounting an attack. Failing to detect enemy reconnaissance and learn about the threat, allows the attacker to enjoy the element of surprise.
For this reason, cyber savvy companies should focus on prevention during the pre-attack phase. But the first thing they should do is assume they will be (or already have been) successfully hacked and prepare accordingly. This also applies to the human threat - or insider threat.
Join The Cipher Brief March 23-25 for a three-day Virtual Cybersecurity Summit co-hosted by Cipher Brief CEO & Publisher Suzanne Kelly and former NSA Deputy Director Rick Ledgett, featuring Microsoft President Brad Smith, FireEye CEO Kevin Mandia, General David Petraeus, former PDDNI Susan Gordon, Silverado Policy Accelerator's Dmitri Alperovitch and a host of other public and private sector experts. Attendance is free and registration is required. Sign up today.
By combining both technical and non-technical methods, organizations will have more effective prevention and incident response when something does occur. Incident response entails mitigating damage from the attack as well as taking preemptive measures and correlating learning from previous attempted attacks.
Using a customized dashboard to integrate evolving events and data, incident response begins with “ingesting” the threat with a security incident management tool. Response continues by escalating the notification by automatically characterizing the incident, assessing the threat, and directing the response. The best platform reduces response time to seconds, with basic triage completed before a human becomes directly involved.
Businesses can effectively reduce the attack space, mitigate risk and conduct more timely and effective incident response by securing servers and routers,
using firewalls and sophisticated web codes, and rigorously applying both patches and back-up protocols.
Far better, of course, is to preempt and eliminate threats in the “left of boom” pre-incident response phase to prevent the enemy from having an opportunity to change, steal, or destroy data. Again, there are proven technical controls to mitigate these scenarios, but businesses tend to skip over the non-technical methods of prevention. Considering the threat of cyber attack as only an IT challenge with technical solutions risks neglecting threats resulting from (what our FBI colleagues like to call) the “skin behind the keyboard.”
We learned from our experience in counterintelligence, the importance of protecting against the insider threat. This results from both unwitting employees who require training to appreciate and defend against the dangers to which they are subjected as well as malicious employees with ill intent. Applying the “need to know” principle with access controls and using technology to conduct regular security checks reduces the attack space. Cross connecting human resources, IT, and security to conduct on-board vetting and follow up engagement with employees has the additional benefit of creating a powerful ethos of security within the company, on which all employees recognize their livelihood depends.
A good strategy to protect the data, money and reputation on which commercial success relies should focus on three key elements:
- Social media bumps and social engineering. Ensure employees are aware of solicitation via social media and networking sites; never share confidential information about your business, passwords, or documents without verifying who is requesting it and why.
- Implement a robust training program. This must focus on enhancing employee awareness, including red flag indicators, the importance of engaging colleagues that appear to be suffering from new stressors, and reporting procedures to report concerns.
- Make yourself a hard target. This may be accomplished by using a layered approach of technology controls to include, mandatory VPN to ensure endpoint integrity, network and sensitive file encryption, role-based access controls, a built-in firewall with strong anti-virus technology; and a clear separation between home and work networks.
The hacker’s mission to exploit, modify, or steal data most often depends on an individual opening a malicious attachment, clicking on a link, or falling for some other ruse, which allows the hacker protected access. We must be as focused as the attacker is on the human element. Organizations must recognize that ignoring the problem doesn’t make it go away and their own employees are their greatest asset and what they should invest in protecting.
Noting the chaos, which would ensue if nefarious hackers simultaneously turned all of the traffic lights green in Manhattan, former Estonian President and Cipher Brief Expert Toomas Hendrik Ilves eloquently framed the challenge as building a capability-based strategy because however expansive our imagination might be, our enemies will always be steps ahead of us in choosing their targets.
Only with the best preparation and defensive measures can we reduce our risk of operating in cyberspace, which Cipher Brief Expert Michael Hayden, the former director of both the CIA and NSA, has compared to swimming in shark-infested waters, where even the dolphins are a threat.
Read more expert-driven national security insight, analysis and perspective in The Cipher Brief.