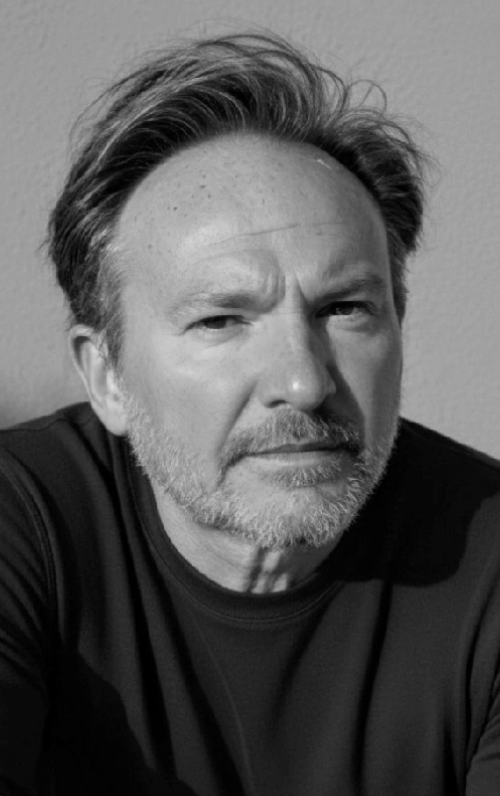
Robert Hannigan is a Principal Member of The Cyber Initiatives Group, powered by The Cipher Brief.
EXPERT PERSPECTIVE — Asked recently what risk he worried about most, alongside Taiwan and Ukraine, Cipher Brief Expert, General Stanley McChrystal said it was cyber security, particularly in the supply chain.
General McChrystal is part of a growing group of the most senior operational and strategic US commanders that include former Chairman of the Joint Chiefs of Staff, Admiral Mike Mullen, in seeing the supply chain threat as existential. Unless the supply chain can be secured, the whole infrastructure on which Western economies rest, not to mention their military defences, will be compromised.
Two factors have brought the otherwise dry subject of supply chain security to the top of the political risk table. One has been the pandemic, in which we have become painfully aware of the fragility of supply chains and the over-dependence of Western countries on external providers, particularly in China. We have also realised how little we actually understand about our supply chains: which companies are in them, who owns them, who controls them and how they can be disrupted.
The other factor has been the SolarWinds attack, almost exactly a year ago. The sophistication of this compromise of the software supply chain, which had probably been active for at least a year before it was discovered, captured headlines around the world. This was partly because SolarWinds Orion was in use by a whole range of government agencies and major companies. More acutely than many other earlier third-party compromises, it illustrated why supply chain companies are such attractive targets: their security is often poor and they represent a softer way into a vast range of customers, including many companies that would in themselves be a hard target. The supply chain is the perfect asymmetric attack.
The Cipher Brief hosts private briefings with the world’s most experienced national and global security experts. Become a member today.
Interest in this is leading to some positive focus.
There are two challenges. The first is visibility. Governments and companies need to understand what the security of their tens of thousands of vendors looks like in real time. That means having the same attitude to the ecosytem of third parties as they would to their own networks. It also means understanding ownership and control and a range of other dependencies. It requires constant monitoring of the supply chain, not occasional compliance exercises. In the end, this will probably need to be required by regulation, but there is no need to wait for that.
Go beyond the headlines with expert perspectives on today’s news with The Cipher Brief’s Daily Open-Source Podcast. Listen here or wherever you listen to podcasts.
Beyond visibility and understanding there needs to be action. We have to move from assessing the risk and admiring the problem to fixing it. This means taking a range of actions from helping vendors to remediate weaknesses to addressing issues of ownership. The UK’s new legislation giving government greater powers to intervene in mergers and acquisitions on national security grounds is long overdue and brings it into line with other Western countries. But these assessment processes will need to become dynamic and constant to reflect the ever-shifting nature of modern vendor ecosystems.
The complexity of the global supply chain is the creation of open economies and democratic societies; but unless it is secured it will ultimately undermine them.
Read more expert-driven national security insights perspective and analysis in The Cipher Brief