
Russia’s Response to U.S. Aid: Shrugs, Disinformation and Warnings of Nuclear War
SUBSCRIBER+ EXCLUSIVE REPORTING — Russia’s reaction to the new infusion of U.S. aid for Ukraine has ranged from shrugs to fury, from warnings of nuclear […] More
We may be frustrated by the state of cybersecurity today, with the attackers getting better and more audacious year after year, but defenders would be even worse off without the dozens of technological, operational and policy innovations generated in the past 50 years. And even as measures once considered new lose their potency, fresh approaches could reinvigorate those tools.
The recently completed New York Cyber Task Force—30 leading experts with backgrounds as cybersecurity executives, technologists, former government officials and academics—recently documented and described these innovations as part of their report on how to create a more defensible cyberspace. The goal, we wrote, was “leverage”—pushing the innovations that provide the most advantage to defenders at the greatest scale and least cost.
Defenders have the most familiarity with technology innovations like passwords and firewalls (inside an enterprise) or automated software updates or end-to-end encryption. All tend to work across cyberspace as a whole.
But operational and policy innovations have played an equally important role. In the 1980s, the Department of Defense had to invent the first Computer Emergency Response Team, after the Morris Worm took down much of the early Internet. Citibank had to invent the role of Chief Information Security Officer, after a major cyber-enabled theft in the mid-1990s. With impetus from the White House, critical infrastructure sectors had to create Information Sharing and Analysis Centers in the late 1990s.
It might sound obvious: only invest in those innovations that payoff. Yet, even a quick review of cybersecurity of the past decade shows many examples of where this simple principle is violated.
Many innovations, in the judgment of the task force and those interviewed, were bad ideas from the start. In the past few years, government arms control experts have introduced rules for applying to offensive cyber technology what’s known as the Wassenaar Arrangement, which promotes transparency and responsibility in transfers of conventional arms and on goods and technologies that have a peaceful purpose but also could serve as weapons.
But the rules generate “negative leverage,” imposing high costs on defenders and placing only minor obstacles in the way of attackers. One cybersecurity company reported that it would have to request at least 1,000 export licenses to comply, instead of the 10 that had been required. Is the requirement to get another 990 export licenses really a smart security investment?
Static and prescriptive “checking-the-box” cybersecurity typically also creates negative leverage. While perhaps satisfying regulators, these protections often force defenders to expend far more effort than it costs attackers to circumvent them.
This was not always the case. Two decades ago, cybersecurity architectures were less complex and threats less varied. So defenses built on static checklists were more effective at keeping out adversaries.
Check-the-box compliance has, in short, gone from essential to albatross. Once a game changer, it has become a drain on the resources of defenders.
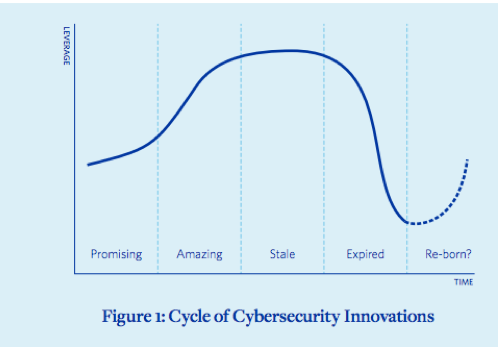
As this example shows, even the best of these innovations have an expiration date. They roll through a cycle of four stages: promising, amazing, stale and expired. They fade as technologies change, adversaries adapt and complexity increases.
The New York Cyber Task Force came across many such innovations that have persisted past their expiration dates. Passwords, by far the most-cited albatross, have long been an insufficient means of authentication when used on their own. Firewalls, intrusion detection and anti-malware may be approaching their expiration date. For the better part of two decades, they have been the basic building blocks of an effective defense. Now, however, they are growing increasingly stale, especially against sophisticated adversaries.
Data-breach notification laws may soon reach their own limits. States enacted these laws to protect the privacy of citizens whose information might have been compromised and to incentivize companies to improve security and avoid the embarrassment of disclosure. But now data breaches are so commonplace—and the public so fatigued by endless notifications—that disclosure is often seen as just another cost of business, with little-to-no leverage.
Most expired innovations should be retired, or at least de-emphasized. But some might gain a new lease on life if it is possible to drastically reduce their costs, use them in combination with other innovations to extend their life, or otherwise revamp them to regain leverage.
Passwords, for example, have regained leverage when combined with a second form of authentication, such as a text to a mobile phone. Even compliance can be reinvigorated when combined with risk-based frameworks. According to a PwC survey, organizations adopting structures like the National Institute of Standards and Technology (NIST) Cybersecurity Framework or ISO 27001 greatly improve their ability to identify and prioritize risks, detect and mitigate threats, and measure progress.
The report of the New York Cyber Task Force argued for a new approach to cyber defense, one that can break the stalemate of the past five decades so that defenders finally have the high ground and can fight with the advantage. This approach does not have to be a highly complex, government-run moon shot or a cyber Manhattan Project. If anything, the world needs a cyber equivalent of famed ecologist Rachel Carson’s 1962 book Silent Spring to reveal to us how precious the Internet is and how our actions are destroying it, and to energize stakeholders to make some hard tradeoffs.
Defense is possible, but only by recognizing the lessons from past innovations and pushing for leverage. Of course, this means nurturing new innovations, but we must also chop down decades of zombie innovations that have been holding us back well past their useful lives.
Jason Healey is Senior Research Scholar at Columbia University’s School of International and Public Affairs. He was executive director of the NY Cyber Task Force, from whose report this piece is drawn. You can follow his tweets on cyber conflict and cyber risk at @Jason_Healey.
Related Articles

SUBSCRIBER+ EXCLUSIVE REPORTING — Russia’s reaction to the new infusion of U.S. aid for Ukraine has ranged from shrugs to fury, from warnings of nuclear […] More

SUBSCRIBER+ EXCLUSIVE REPORTING — When Chinese President Xi Jinping came to San Francisco last November to meet with President Joe Biden, Chinese pro-democracy activists in […] More

SUBSCRIBER+EXCLUSIVE EXPERT PERSPECTIVE — More than two years after its withdrawal from Afghanistan, the U.S. still does not have a clear way forward in the […] More

SUBSCRIBER+ EXCLUSIVE REPORTING — Ukrainians greeted Saturday’s long-awaited House passage of $60.8 billion in aid with justifiable jubilation. For months, their soldiers, civilians, and political […] More

SUBSCRIBER+ EXCLUSIVE REPORTING — A race for control of space is underway, and just as on earth, the U.S. and China are the top competitors. […] More

SUBSCRIBER+ EXCLUSIVE REPORTING — For nearly a week, the Middle East and much of the world were on a knife’s edge, waiting for a promised […] More
Search