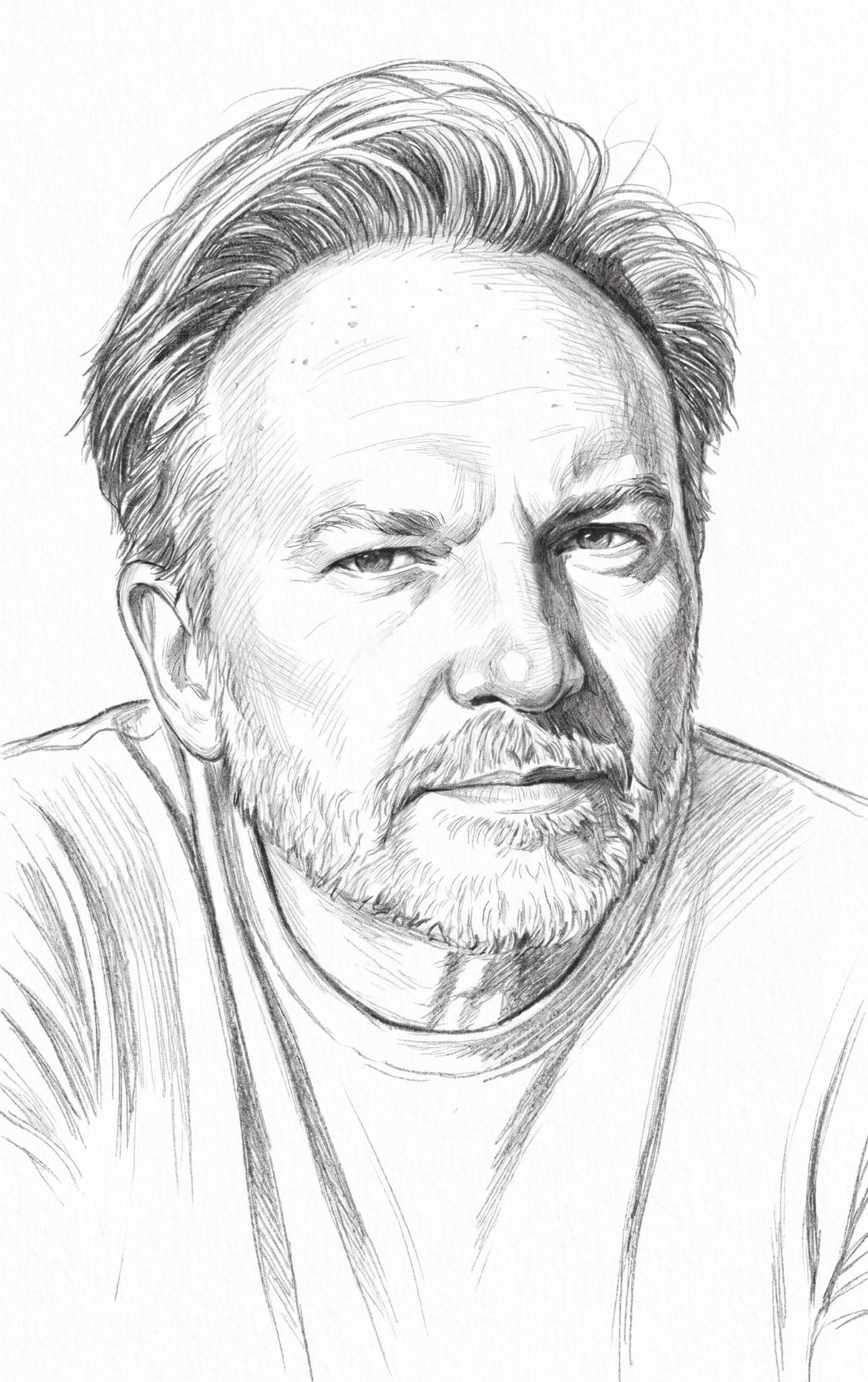
Do you bring your own laptop to the office, or does your phone connect to your company’s Wi-Fi network? If so, then you need to be concerned about endpoint security. The rise of bring-your-own-device (BYOD) culture in many organizations has created a multitude of new entry points for cyber-attackers, but there are a number of ways to protect yourself. The Cipher Brief spoke with Doug Cahill, a senior analyst at Enterprise Strategy Group, about how endpoint security is changing to counter the ever-evolving cyber threat. He says that the technology needed to counter endpoint threats is improving, but educating employees about good cyber habits is the most effective practice for all companies.
The Cipher Brief: What role does endpoint security play in protecting organizations from cyber threats? What mistakes do companies typically make in regards to managing their endpoint security, and how can these mistakes be avoided?
Doug Cahill: As the most common attack vector, the endpoint plays a central role in the cybersecurity kill chain from the delivery to command and control stages. Human gullibility is a vulnerability that is easily and regularly exploited with methods such as spear phishing and web site drive-bys. After Operation Aurora in 2010 and the advent of advanced persistent threats (APTs), many organizations indexed on a network-centric security model to detect malware on the wire but failed to secure the endpoint entry point, resulting in attacks already moving laterally in their environment by the time of detection. In such a post-compromise situation, security teams are in a reactive posture, scrambling to avoid an incident by preventing, or at least minimizing, data exfiltration.
Given this reality, organizations should be more proactive earlier on in the kill chain by securing endpoints with preventative controls to reduce attack surface area and sensors, which continuously monitor and record system activity to expedite detection and response. Such an advanced endpoint security solution will work in concert with network security controls by, for example, exchanging and leveraging threat intelligence that is made contextual and thus actionable.
TCB: What are some best practices in regards to endpoint security? Which sectors or industries are most vulnerable to threats from this area, and why?
DC: Regular end-user cybersecurity awareness training to educate users about spear phishing and safe web browsing habits is a best practice all companies should employ. The effectiveness of such awareness training should be tested via red team exercises to challenge not only an organization’s security technologies but also end-user compliance with corporate security policies. This form of “trust, but verify” should be measured, communicated, and repeated for currency. Updating endpoint-resident software with a history of vulnerabilities that have been successful exploited is another immutable best practice.
As we saw in 2015, health care organizations are especially susceptible to cybersecurity attacks, driven by bad actor interest in monetizing stolen protected health information (PHI) data vies-a-vies fraudulent claims. Companies that hold credit card data continue to be at risk independent of PCI DSS compliance, the 12 prescriptive requirements of which are representative of a solid framework but not a conclusive solution set. As the definition of an endpoint expands from laptops and desktops to mobile devices, companies with a liberal BYOD policy should also consider monitoring and enforcing network access as well as cloud access security brokers for visibility and control over the use of software as a service (SaaS) applications.
TCB: How have the threats to endpoint security changed over the last few years? How do you anticipate that they will change moving forward?
How has endpoint security changed to counter the threats mentioned above? What trends have you seen in endpoint security management, and how do you see it changing in the future?
DC: The seemingly legitimate nature of socially engineered spear phishing attacks continues to be the most common and thus most effective threat to endpoint security. Such attacks utilize a variety of methods to turn an end-user into an unwitting proxy for a bad actor. These methods include website drive-by downloads of malicious binary payloads as well as a notable increase in weaponized content, such as PDFs, that can be especially difficult to detect. Enterprise Strategy Group expects these types of attacks to persist unabated, with the prevalence of ransomware continuing to be highly problematic for enterprises and consumers alike.
Fortunately, there have been appreciable advances in prevention technologies that can protect endpoints from new and previously unknown malware. These solutions use a variety of methods including, machine learning to inspect binaries prior to execution, application behavior monitoring to detect techniques known to be employed by malware writers, and inspecting file-less and sometime memory-resident content for threats to thwart a variety of attacks. But no prevention approach will be completely effective in this cat and mouse game between attacker and defender, so some organizations are leveraging endpoint detection and response (EDR) solutions for post-compromise situations, which provide forensic capture and play back capabilities to expedite remediation and shorten dwell time.
Endpoint security is a market in transition and one which organizations should spend the time investigating as part of a strategic initiative to secure a highly vulnerable part of their infrastructure.