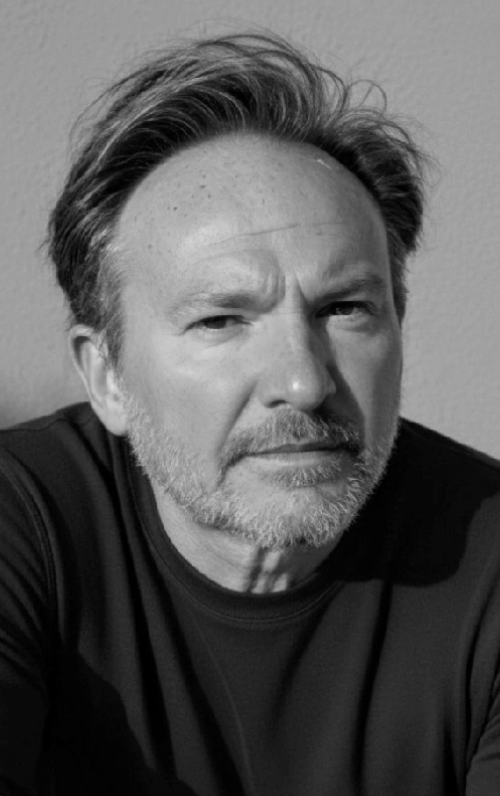
As part of a week-long series focused on Mapping China’s Ambitions, The Cipher Brief is partnering with Harvard Research Fellow and former British diplomat Jamie Burnham to explore China’s threat vectors, how it is organizing to win, what a government ecosystem looks like and the impact that international collaboration will have in the future.
Yesterday in The Cipher Brief, Jamie explored China’s broad ambitions and threat vectors, today, he focuses on how Beijing is organizing against those ambitions and threat vectors.
Keep reading...Show less