DEEP DIVE — From stolen military credentials to AI-generated personas seamlessly breaching critical infrastructure, digital identity fraud is rapidly escalating into a frontline national security threat. This sophisticated form of deception allows adversaries to bypass traditional defenses, making it an increasingly potent weapon.
The 2025 Identity Breach Report, published by AI-driven identity risk firm Constella Intelligence, reveals a staggering increase in the circulation of stolen credentials and synthetic identities. The findings warn that this invisible epidemic, meaning it's harder to detect than traditional malware, or it blends in with legitimate activity, is no longer just a commercial concern—it now poses a serious threat to U.S. national security.
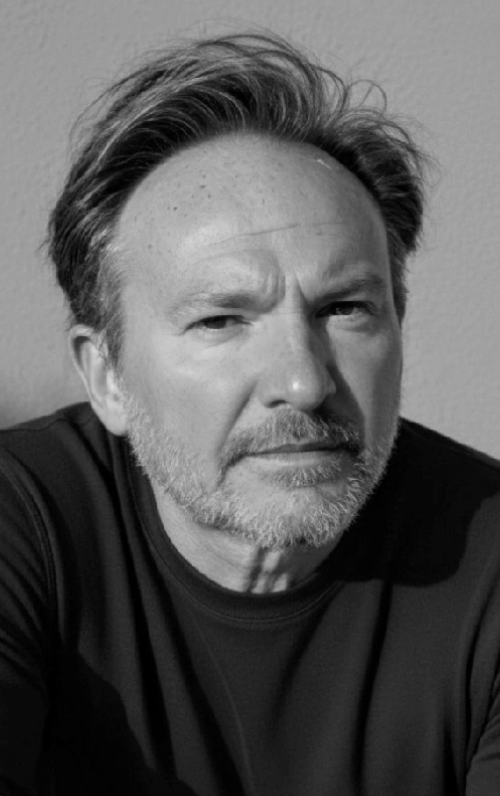
“Identity verification is the foundation of virtually all security systems, digital and physical, and AI is making it easier than ever to undermine this process,” Mike Sexton, a Senior Policy Advisor for AI & Digital Technology at national think tank Third Way, tells The Cipher Brief. “AI makes it easier for attackers to simulate real voices or hack and steal private credentials at unprecedented scale. This is poised to exacerbate the cyberthreats the United States faces broadly, especially civilians, underscoring the danger of Donald Trump’s sweeping job cuts at the Cybersecurity and Infrastructure Security Agency.”
The Trump administration’s proposed Fiscal Year 2026 budget would eliminate 1,083 positions at CISA, reducing staffing by nearly 30 percent from roughly 3,732 roles to around 2,649.
Save your virtual seat now for The Cyber Initiatives Group Winter Summit on December 10 from 12p – 3p ET for more conversations on cyber, AI and the future of national security.
The Industrialization of Identity Theft
The Constella report, based on analysis of 80 billion breached records from 2016 to 2024, highlights a growing reliance on synthetic identities—fake personas created from both real and fabricated data. Once limited to financial scams, these identities are now being used for far more dangerous purposes, including espionage, infrastructure sabotage, and disinformation campaigns.
State-backed actors and criminal groups are increasingly using identity fraud to bypass traditional cybersecurity defenses. In one case, hackers used stolen administrator credentials at an energy sector company to silently monitor internal communications for more than a year, mapping both its digital and physical operations.
“In 2024, identity moved further into the crosshairs of cybercriminal operations,” the report states. “From mass-scale infostealer infections to the recycling of decade-old credentials, attackers are industrializing identity compromise with unprecedented efficiency and reach. This year’s data exposes a machine-scale identity threat economy, where automation and near-zero cost tactics turn identities into the enterprise’s most targeted assets.”
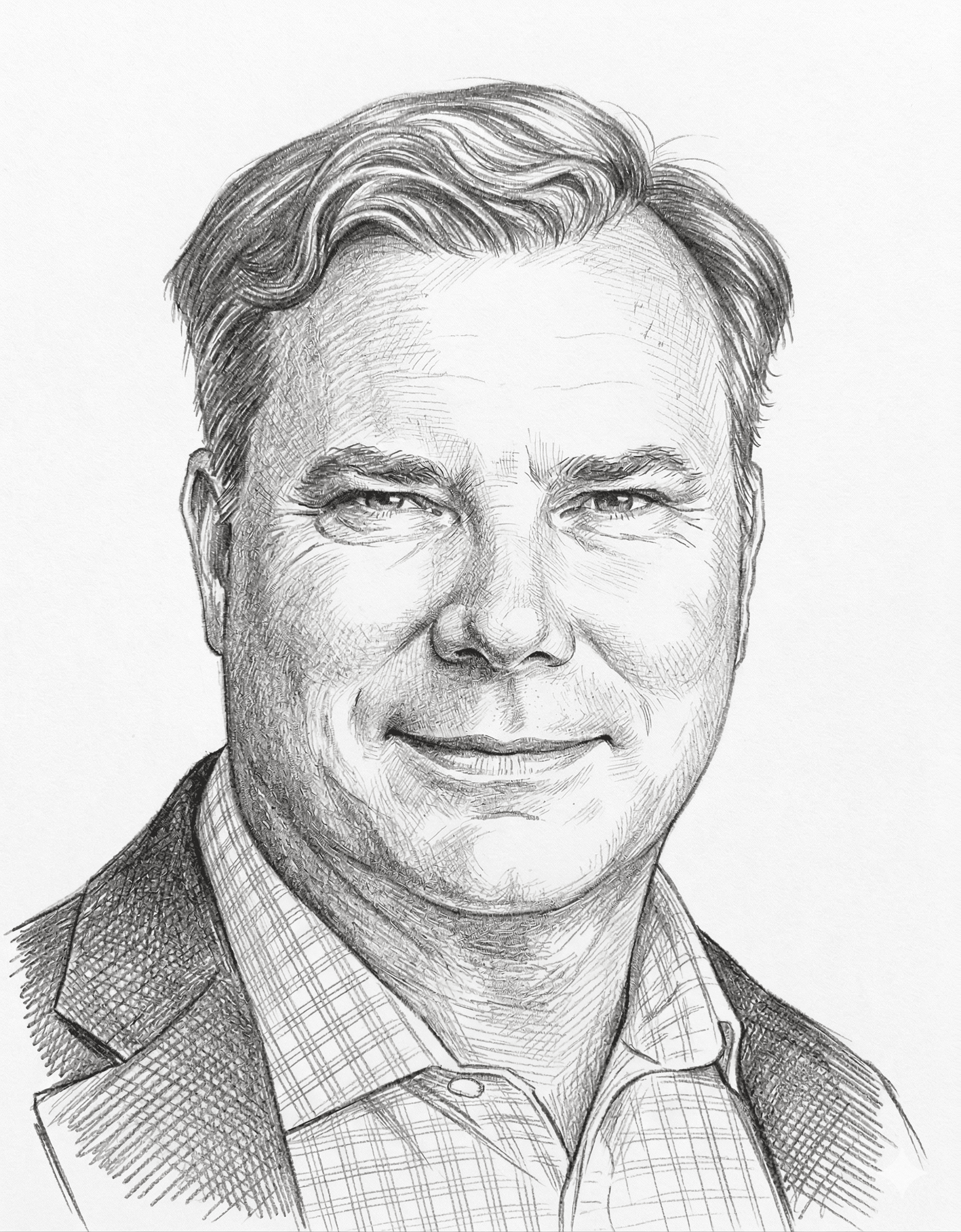
Dave Chronister, CEO of Parameter Security and a prominent ethical hacker, links the rise in identity-based threats to broader social changes.
“Many companies operate with teams that have never met face-to-face. Business is conducted over LinkedIn, decisions authorized via messaging apps, and meetings are held on Zoom instead of in physical conference rooms,” he tells The Cipher Brief. “This has created an environment where identities are increasingly accepted at face value, and that’s exactly what adversaries are exploiting.”
When Identities Become Weapons
This threat isn’t hypothetical. In early July, a breach by the China-linked hacking group Volt Typhoon exposed Army National Guard network diagrams and administrative credentials. U.S. officials confirmed the hackers used stolen credentials and “living off the land” techniques—relying on legitimate admin tools to avoid detection.
In the context of cybersecurity, “living off the land” refers to attackers (like the China-linked hacking group Volt Typhoon) don't bring their own malicious software or tools into a compromised network. Instead, they use the legitimate software, tools, and functionalities that are already present on the victim's systems and within their network.
“It’s far more difficult to detect a fake worker or the misuse of legitimate credentials than to flag malware on a network,” Chronister explained.
Unlike traditional identity theft, which hijacks existing identities, synthetic identity fraud creates entirely new ones using a blend of real and fake data—such as Social Security numbers from minors or the deceased. These identities can be used to obtain official documents, government benefits, or even access secure networks while posing as real people.
“Insider threats, whether fully synthetic or stolen identities, are among the most dangerous types of attacks an organization can face, because they grant adversaries unfettered access to sensitive information and systems,” Chronister continued.
Insider threats involve attacks that come from individuals with legitimate access, such as employees or fake identities posing as trusted users, making them harder to detect and often more damaging.
Constella reports these identities are 20 times harder to detect than traditional fraud. Once established with a digital history, a synthetic identity can even appear more trustworthy than a real person with limited online presence.
“GenAI tools now enable foreign actors to communicate in pitch-perfect English while adopting realistic personas. Deepfake technology makes it possible to create convincing visual identities from just a single photo,” Chronister said. “When used together, these technologies blur the line between real and fake in ways that legacy security models were never designed to address.”
Washington Lags Behind
U.S. officials acknowledge that the country remains underprepared. Multiple recent hearings and reports from the Department of Homeland Security and the House Homeland Security Committee have flagged digital identity as a growing national security vulnerability—driven by threats from China, transnational cybercrime groups, and the rise of synthetic identities.
The committee has urged urgent reforms, including mandatory quarterly “identity hygiene” audits for organizations managing critical infrastructure, modernized authentication protocols, and stronger public-private intelligence sharing.
Meanwhile, the Defense Intelligence Agency’s 2025 Global Threat Assessment warns:
“Advanced technology is also enabling foreign intelligence services to target our personnel and activities in new ways. The rapid pace of innovation will only accelerate in the coming years, continually generating means for our adversaries to threaten U.S. interests.”
An intelligence official not authorized to speak publicly told The Cipher Brief that identity manipulation will increasingly serve as a primary attack vector to exploit political divisions, hijack supply chains, or infiltrate democratic processes.
Need a daily dose of reality on national and global security issues? Subscriber to The Cipher Brief’s Nightcap newsletter, delivering expert insights on today’s events – right to your inbox. Sign up for free today.
Private Sector on the Frontline
For now, much of the responsibility falls on private companies—especially those in banking, healthcare, and energy. According to Constella, nearly one in three breaches last year targeted sectors classified as critical infrastructure.
“It's never easy to replace a core technology, particularly in critical infrastructure sectors. That’s why these systems often stay in place for many years if not decades,” said Chronister.
Experts warn that reacting to threats after they’ve occurred is no longer sufficient. Companies must adopt proactive defenses, including constant identity verification, behavioral analytics, and zero-trust models that treat every user as untrusted by default.
However, technical upgrades aren’t enough. Sexton argues the United States needs a national digital identity framework that moves beyond outdated systems like Social Security numbers and weak passwords.
“The adherence to best-in-class identity management solutions is critical. In practice for the private sector, this means relying on trusted third parties like Google, Meta, Apple, and others for identity verification,” he explained. “For the U.S. government, these are systems like REAL ID, ID.me, and Login.gov. We must also be mindful that heavy reliance on these identity hubs creates concentration risk, making their security a critical national security chokepoint.”
Building a National Identity Defense
Some progress is underway. The federal Login.gov platform is expanding its fraud prevention capabilities, with plans to incorporate Mobile Driver’s Licenses and biometric logins by early 2026. But implementation remains limited in scale, and many agencies still rely on outdated systems that don’t support basic protections like multi-factor authentication.
“I would like to see the US government further develop and scale solutions like Login.gov and ID.me and then interoperate with credit agencies and law enforcement to respond to identity theft in real time,” Sexton said. “While securing those systems will always be a moving target, users’ data is ultimately safer in the hands of a well-resourced public entity than in those of private firms already struggling to defend their infrastructure.”
John Dwyer, Deputy CTO of Binary Defense and former Head of Research at IBM X-Force, agreed that a unified national system is needed.
“The United States needs a national digital identity framework—but one built with a balance of security, privacy, and interoperability,” Dwyer told The Cipher Brief. “As threat actors increasingly target digital identities to compromise critical infrastructure, the stakes for getting identity right have never been higher.”
He emphasized that any framework must be built on multi-factor authentication, phishing resistance, cryptographic proofs, and decentralized systems—not centralized databases.
“Public-private collaboration is crucial: government agencies can serve as trusted identity verification sources (e.g., DMV, passport authorities), while the private sector can drive innovation in delivery and authentication,” Dwyer added. “A governance board with cross-sector representation should oversee policy and trust models.”
Digital identities are no longer just a privacy concern—they’re weapons, vulnerabilities, and battlegrounds in 21st-century conflict. As foreign adversaries grow more sophisticated and U.S. defenses lag behind, the question is no longer if, but how fast America can respond.
The question now is whether the United States can shift fast enough to keep up.
Read more expert-driven national security insights, perspective and analysis in The Cipher Brief because National Security is Everyone’s Business.