
Day 3: Dispatch from RSA Conference
This week I am attending the RSA Conference, a global convention bringing together government and business approaches to secure the digital channels people depend on […] More

This week I am attending the RSA Conference, a global convention bringing together government and business approaches to secure the digital channels people depend on […] More

If you missed our previous dispatch, I am attending the annual RSA Conference in San Francisco, a global event where private and public sectors come […] More
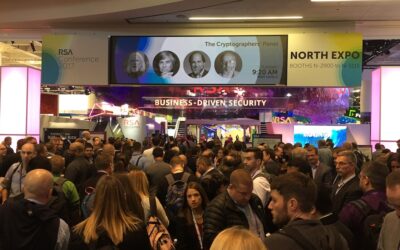
This week I’m attending the annual RSA Conference in San Francisco, where government and industry leaders have come together to discuss the looming challenges and […] More

Since the first CIA Predator drone strike in October 2001, the United States, among others, has sought to expand the technology to facilitate remote warfare. […] More

Remotely controlled aircraft, or drones, have long become common in military settings—possibly most infamously pictured as a U.S. Predator launching Hellfire missiles at suspected terrorists […] More

While receiving significant publicity from global media, the rise of the humanitarian drone is so far more of a whimper than a bang. This article […] More

The impact that the Snowden revelations had on private businesses is one of the most overlooked stories in the Snowden saga, particularly the impact on […] More

The cybersecurity industry is currently enamored with concepts of autonomous defense, including elements of machine learning, behavioral analytics, and artificial intelligence—and rightly so. Programed to […] More

Many view cybersecurity as passively blocking attempts to breach networks, but security experts have long advocated more active measures in defense of sensitive networks. Advances […] More

We live in an age where what used to be the figment of science fiction is now a reality, changing the way people go about […] More

With cybercrime expected to reach costs nearing $2 trillion by 2019, firms are urgently seeking ways to better defend their networks from the harmful impacts […] More

Cybersecurity is often discussed in relation to the major global powers: China’s economic espionage, Russian influence operations, and U.S. dragnet global surveillance to thwart terrorism. […] More

Recent years have witnessed a series of increasingly audacious and unprecedented cyber attacks, leading up to the recent accusations of Russian hacking throughout last year’s […] More

Cyber is emerging as Iran’s weapon of choice for dealing with both domestic and foreign opponents. For more than a decade, the Islamic Republic has […] More

The cultural shift stemming from a “need-to-know” to a “need-to-share” atmosphere in the intelligence community in the wake of 9/11 has been necessary to operate […] More

For years, the easiest avenue to conduct a cyber attack against a business or an organization was social engineering attacks via emails. While still a […] More

Distinguishing between whistleblowers who want to point out and fix problems within the intelligence community and employees who want to damage national security will demand […] More

When defense contractor Harold Martin was charged with the alleged theft of highly classified documents from the National Security Agency (NSA), federal prosecutors deemed the […] More
Search