
Leaving the Oil Spigot Open
On April 17, the thirteen members of OPEC (Organization of Petroleum Exporting Countries) and five other major producers met in Doha to negotiate a long-awaited […] More

On April 17, the thirteen members of OPEC (Organization of Petroleum Exporting Countries) and five other major producers met in Doha to negotiate a long-awaited […] More

The international oil market has been in a state of chaos over the past two years, as prices dropped more than 75 percent. Last month, […] More

In November 2014, the thirteen members of the Organization for Petroleum Exporting Countries (OPEC) shocked oil markets by announcing that, in order to “restore market […] More

What do you use your phone for in a given day? Texting, checking the news, social media, banking, getting directions, playing games – most people […] More

Bring-your-own-device culture is very convenient, but with a growing amount of malware targeting mobile devices, it is also creating new vulnerabilities. The Cipher Brief spoke […] More

As malware continues to grow and change, the number and types of at-risk devices will do the same. Currently, malware oriented towards mobile devices is […] More

Strikes and continuous violence have strained the fresh Aleppo cease-fire the United States and Russia brokered this week, leaving experts doubtful any cessation of hostilities […] More

It’s the year 2011 and the “Arab Spring” has begun in Cairo, Egypt. Guests at a nearby hotel are panicking and desperate to leave, and […] More

China sent a major signal to the U.S. last week, when it turned away the USS John C. Stennis aircraft carrier and accompanying vessels from […] More

China’s President Xi Jinping has committed himself to the country’s development as a maritime power and to protecting its sovereignty. One can reasonably assume that […] More

China’s neighbors are gravely concerned about what they see as a clear and determined strategy being implemented by Xi Jinping, the leader of the Chinese […] More

Broadcasting brutal murder videos, enslaving religious minorities, training and deploying child soldiers, carrying out suicide bombings at crowded intersections – these are just some of […] More

Our basic understanding of the Islamic State’s ambitions, and its justifications of those ambitions, remains muddled. “Remaining and expanding” and “a caliphate on the Prophet […] More

Is ISIS Islamic? Probably not. Is it Islamist? Definitely. An Islamist is one who believes in a version of Islam which would impose a politicized […] More

Latin American countries have a long history of swift regime change, either by coup or by legitimate institutional processes. The impetus is typically economic decline. […] More
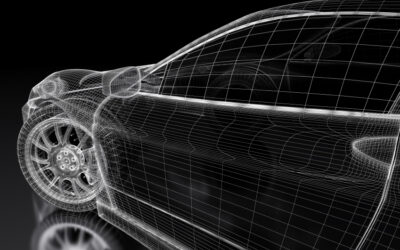
Everyone knows that they need to protect their computers from hackers, but have you ever considered what would happen if someone hacked your car? Automakers […] More

It is hard to miss the frightening headlines about car hacking scenarios. But in reality, there’s more to automotive cyber security. Hackers may be individuals […] More

Cars, like many other everyday objects, are now more connected to wireless networks than ever before – and this has caused a corresponding rise in […] More
Search