
Cybersecurity Official: Many Water Facilities Still Unaware of Threat – and Unprepared
SUBSCRIBER+ EXCLUSIVE INTERVIEW — Last week The Cipher Brief published a look at the threat to the nation’s water supply posed by cyberattacks – an […] More
“The Cipher Brief has become the most popular outlet for former intelligence officers; no media outlet is even a close second to The Cipher Brief in terms of the number of articles published by formers.” —Sept. 2018, Studies in Intelligence, Vol. 62
Access all of The Cipher Brief’s national security-focused expert insight by becoming a Cipher Brief Subscriber+ Member.
Related Articles

SUBSCRIBER+ EXCLUSIVE INTERVIEW — Last week The Cipher Brief published a look at the threat to the nation’s water supply posed by cyberattacks – an […] More

SUBSCRIBER+EXCLUSIVE ANALYSIS — While top cybersecurity officials sound the alarm over intrusions by Russia, China and individual hackers into U.S. critical infrastructure, they’ve noticed another […] More
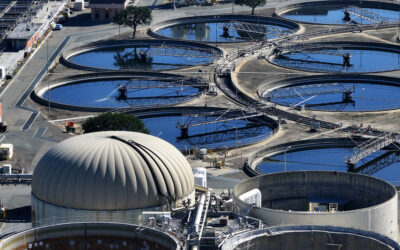
BOTTOM LINE UP FRONT — It’s a serious threat to the nation’s critical infrastructure that not enough people are talking about. That’s the view of […] More

SUBSCRIBER+ EXCLUSIVE REPORTING — A race for control of space is underway, and just as on earth, the U.S. and China are the top competitors. […] More

SUBSCRIBER+ EXCLUSIVE REPORTING — With artificial intelligence getting smarter every day, cybersecurity experts, election officials and voters have been fretting about the possibility that malicious […] More

SUBSCRIBER+ EXCLUSIVE — When U.S. and British officials filed charges of cyberespionage and imposed sanctions against China Monday, for a campaign which they said had […] More
Search