
NATO and Cyberwar Strategy: Proceed with Caution
NATO has much to discuss at its annual summit in Warsaw on July 8 – 9. From the implications of the UK’s decision to exit […] More

NATO has much to discuss at its annual summit in Warsaw on July 8 – 9. From the implications of the UK’s decision to exit […] More

On Tuesday, it came to light that the Democratic National Convention’s (DNC) network had been breached by not one, but two different hacker groups that […] More

The breach of the Democratic National Committee (DNC) by hackers believed to be affiliated with the Russian government is raising concerns about foreign interference in […] More

Networked medical devices are becoming steadily more common, and they are making things easier for both patients and healthcare providers. However, there is an accompanying […] More

In January, the CEO of American Superconductor publicly detailed how traditional economic espionage methods carried out by a small Chinese firm resulted in over a […] More

Like a slow-motion tsunami, the Internet of Things (IoT) is continuing to wash over an ever-greater portion of our lives, and now, our bodies. The […] More

The Internet of Things is continuing to grow and expand, with some aspects of smart technology even entering the human body through pacemakers and other […] More
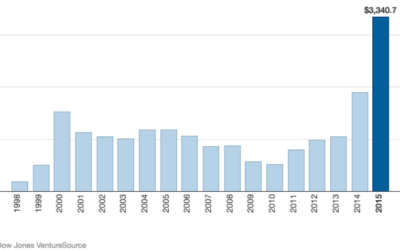
The cybersecurity startup market has been hot. On fire is probably more accurate. The graph above shows how investment has been ramping up over the […] More

On May 10, 2016, Peter Romar, a hacker associated with the Syrian Electronic Army, appeared in a U.S. courtroom after his extradition from Germany to […] More
Everyone knows that they need to protect their computers from hackers, but have you ever considered what would happen if someone hacked your car? Automakers […] More

It is hard to miss the frightening headlines about car hacking scenarios. But in reality, there’s more to automotive cyber security. Hackers may be individuals […] More

Cars, like many other everyday objects, are now more connected to wireless networks than ever before – and this has caused a corresponding rise in […] More

Stranded during a historic Washington-area blizzard in February 2010, a U.S. soldier embarked on a mission that he had sworn to not fulfill: “…I joined […] More
When it comes to Silicon Valley buzzwords, “the cloud” is one of the most ubiquitous and one of the most misunderstood. The cloud is essentially […] More

Access to cloud-based infrastructure has revolutionized how businesses store and work with their data, but the convenience of cloud-based systems is not without risk. The […] More

Way back in the 18th century, Ben Franklin said, “Distrust and caution are the parents of security.” That insight is entirely appropriate in the 21st […] More

It seems like the cyber domain has recently been awash in controversy. From major hacks that compromise the information of millions of people, to bitter […] More

Despite being the wellspring for cutting-edge technology brands such as Samsung, Sony, and HTC, Asia has proven to be less adept at managing a different […] More
Search