
Heading Off State-Sponsored Hacker Attacks
Time and time again companies, organizations, and government agencies have proven that they can’t completely secure their computer networks from hackers – particularly nation-states with […] More

Time and time again companies, organizations, and government agencies have proven that they can’t completely secure their computer networks from hackers – particularly nation-states with […] More

Disruptive and intrusive cyber activity pervades much of modern international relations. The trend towards the jockeying for global influence and geopolitical positioning through cyber means […] More
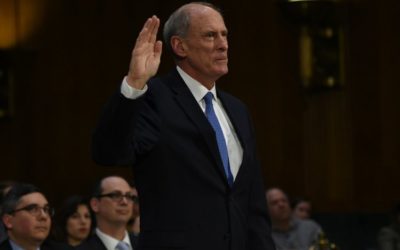
Dan Coats, Director of National Intelligence, told the Aspen Security Forum today that he believes the U.S. national security community lacks the capability to prevent […] More


Tradecraft. A term popularized in the novels of John le Carré, but practiced by spies throughout history. Tradecraft includes a number of methodologies, ranging from […] More

Intelligence officers must often use a false identity — a legend or cover. How has social media and digital technology changed how they create and […] More

Intelligence officers’ tradecraft is highly guarded for good reason. One of its most important aspects is establishing a cover identity so foreign governments and hostile […] More

The main loss from the departure of Chris Painter, America’s top cyber diplomat, will not be the loss of one of the top U.S. civil […] More

Despite the many logistical and operational challenges of a transition, many acknowledge that U.S. Cyber Command must eventually separate from the National Security Agency. According […] More

Reports of intrusions into industrial control systems (ICS) broke late last week – this time in several U.S. power plants, including the Wolf Creek nuclear […] More

Relations between the United States and North Korea hit a new low following Pyongyang’s test of an ICBM July 4. With a range of up […] More

In May, the U.S. Ground-based Midcourse Defense system – the GMD – successfully intercepted a mock ICBM in a critical test of the U.S. missile […] More

The Pentagon’s missile defense review is now underway, incorporating mandates from both the White House and Congress. One of its considerations, at presidential direction, is […] More

As the dust settles on last Tuesday’s NotPetya malware outbreak, it is increasingly evident that this was not a ransomware, money-making attack at all; rather […] More

Intelligence Advanced Research Projects Activity Director Jason Matheny worries a lot about national security risks that probably aren’t headlining many lists of pressing threats to […] More

It’s Labor Day, September 4, 2017, and the National Security Agency has just intercepted communications between the senior leadership of the Iranian Revolutionary Guard Corps, […] More

Last February, President Donald Trump issued an Executive Order calling on the Department of Treasury to review the 2010 Dodd-Frank Wall Street Reform and Consumer Protection Act […] More

With the advent of digital communications, people thousands of miles apart can engage with each other seamlessly, and businesses can operate at a scale previously […] More
Search