
Existing International Law Applies Online and Offline
A group of international law experts met in Tallinn, Estonia, after the 2007 onslaught of cyber attacks against sites in the country, to create the […] More

A group of international law experts met in Tallinn, Estonia, after the 2007 onslaught of cyber attacks against sites in the country, to create the […] More

Cyber operations remain at the forefront of confrontations between the West and Moscow as relations continue to deteriorate. Russia asserted itself in 2007 with “patriotic […] More

Understanding the Russian criminal underground is essential when discussing Russian proxies in cyberspace. How do cybercriminal entities interact with each other and what is their […] More

What if network defenders knew that a cyber operation occurred during Moscow business hours, that it involved a Russian IP address, and that the cyber […] More

Lockheed Martin is in the midst of a lucrative deal to move production of America’s venerable F-16 fighter jet to India. While there are no […] More

India’s growing wealth and regional influence has afforded it the ability and cause to develop a more technologically advanced defense industry. However, since India opened […] More

After decades of government support and investment, the South Korean defense industry can now produce advanced tanks, ships, and submarines and is poised to become […] More

For many, cybersecurity is a technical problem and therefore requires technical solutions. But for policymakers and the national security community, a key takeaway from this […] More

This week I am attending the RSA Conference, a global convention bringing together government and business approaches to secure the digital channels people depend on […] More

The cybersecurity industry, much like other sectors, is dealing with an influx of data. In response, security experts hope to harness the power of artificial […] More

This week I am attending the RSA Conference, a global convention bringing together government and business approaches to secure the digital channels people depend on […] More

If you missed our previous dispatch, I am attending the annual RSA Conference in San Francisco, a global event where private and public sectors come […] More
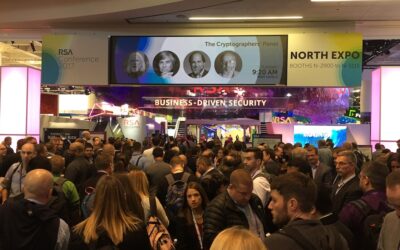
This week I’m attending the annual RSA Conference in San Francisco, where government and industry leaders have come together to discuss the looming challenges and […] More

Since the first CIA Predator drone strike in October 2001, the United States, among others, has sought to expand the technology to facilitate remote warfare. […] More

Remotely controlled aircraft, or drones, have long become common in military settings—possibly most infamously pictured as a U.S. Predator launching Hellfire missiles at suspected terrorists […] More

While receiving significant publicity from global media, the rise of the humanitarian drone is so far more of a whimper than a bang. This article […] More

We live in an age where what used to be the figment of science fiction is now a reality, changing the way people go about […] More

The cybersecurity industry is currently enamored with concepts of autonomous defense, including elements of machine learning, behavioral analytics, and artificial intelligence—and rightly so. Programed to […] More
Search