Join us this week Tuesday – Thursday for The Cipher Brief’s Cybersecurity Summit featuring leaders from the public and private sectors, including Microsoft President Brad Smith, FireEye CEO Kevin Mandia, and 28 other cyber security thought leaders, including today’s author, Andrew Stewart. Attendance is free and registration is required.
Executing Commander’s Intent at Machine Speed for Cyber Operations
Three Integrated Technology Essentials
Andrew D. Stewart, National Security and Sr. Government Strategist, Cisco Systems

Andrew D. Stewart is a National Security and Government Senior Strategist for Cybersecurity at Cisco Systems, Inc. He works across Cisco’s Global Government practice but focuses primarily on National Defense and Intelligence. He served almost 30 years in the U.S. Navy where he last served as the Chief of Cyber Operations for Fleet Cyber Command/U.S. TENTH Fleet. He also served as the Commanding Officer and Program Manager of the Navy Cyber Warfare Development Group (NCWDG).
The Need. Decision advantage for the federal government and in DoD combined cyber operations results from the secure, seamless, and rapid maneuver of data and information. Rapid adoption and integrated implementation three technologies across federal and DoD networks must be realized in order to execute cyber operations according to Commander’s Intent—at machine speed. These technologies, integrated tightly together, offer the opportunity for the government to implement revolutionary cyber operations capabilities from edge-to-cloud and produce improved, data-enabled mission results. The scalable and seamless integration of: (1) advanced identity services, (2) software-defined networking, and (3) hybrid cloud capabilities form a Commander’s Intent-driven cyber platform that is realized in an architecture founded on zero trust principles and that operates at machine speed – ensuring cybersecurity and providing decision advantage for the Nation.
Several artificial intelligence and data strategy documents—spanning federal government agencies, especially the DoD—all recognize that certain key building blocks and platforms must be put in place to scale and democratize access to data and unlock artificial intelligence capabilities—including the means to have “common foundation of shared data, reusable tools, frameworks and standards, and cloud and edge services.” Uniformly, the recognition that getting and using more data from the edge can make government agencies more efficient and will provide the Nation decision advantage. The demand to generate, access and consume more data from the edge has never been greater and this demand is driving the need for more innovation to support government‑wide secure cyber operations. This is quickly apparent from a cursory review of today’s topical programs relevant to the federal space that include: mobility (5G & Wi-Fi 6), mobile workforce, IOT / ICS, digital transformation (Depots, Shipyards, Manufacturing), Agency-wide Data Strategies, DoD’s JADC2, CMMC & DIB, and TIC-3.0. This list alone allows one to conclude that edge, datacenter, private-cloud, and public-cloud are all converging into one combined hybrid cloud operating environment. This emerging environment – necessitated by users who requires access to data and applications from anywhere, on any device – mandates a security approach that is built on a software defined perimeter built on these three technology essentials.
Hence, at the heart of the need for innovation is an increased demand for the sharing of data and applications – from anywhere – while, simultaneously, the size/scale of government networks, networking, and hybrid cloud adoption are exploding without a proportionate growth in the IT resources to support the cyber operational demand. If the network continues to grow exponentially and must function as the medium of maneuver for data and applications that provide the government decision advantage, then the government must deploy revolutionary innovations to reinvent the network as an integrated platform for cyber operations. Therefore, these three integrated technologies are absolutely essential to support the Nation’s growing needs to simultaneously leverage and protect data.
Join The Cipher Brief March 23-25 for a three-day Virtual Cybersecurity Summit featuring leaders from the public and private sectors, including Microsoft President Brad Smith, FireEye CEO Kevin Mandia, and a host of other public and private sector experts. The Summit is co-hosted by Cipher Brief CEO & Publisher Suzanne Kelly and former NSA Deputy Director Rick Ledgett. Attendance is free and registration is required.
The Vision. A Commander’s Intent-driven, hybrid cloud network capable of providing the government with a secure medium of maneuver for data and applications – providing decision advantage. An intent-driven network is made possible through the tight integration of advanced user/device identity services, software-defined networking, and hybrid cloud technologies. These integrated capabilities allow for a revolution in cyber operations to realize a government cyber platform that delivers integrated network operations with visibility, agility, and security—all founded on a zero trust philosophy. With such an approach, a least privilege access, intent-driven policy is applied to every OT device, all users and all devices, and on each and every application workload. It is the tight integration of advanced identity services, software-defined networking, and hybrid cloud capabilities that makes this vision possible.
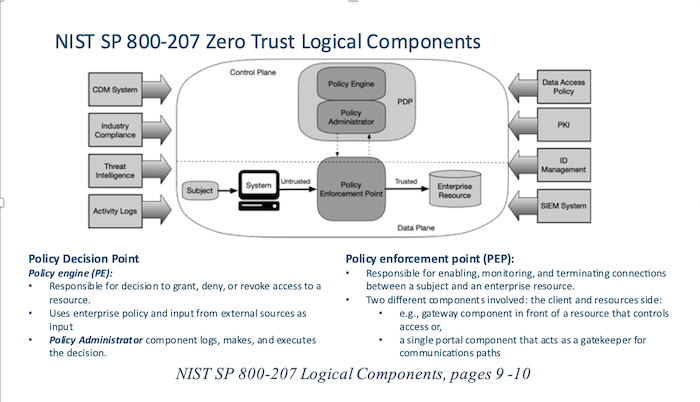
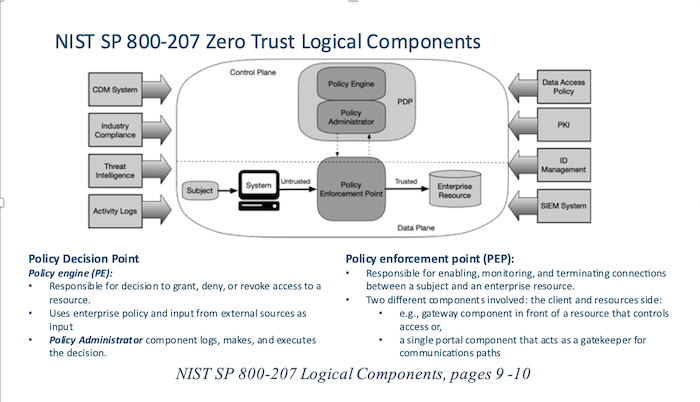
Taking a zero trust philosophic approach and following the guidelines of NIST SP 800-207, implementation of a software-defined wide-area network provides the means for granular access control and logical micro segmentation by weaving layers of the network into a policy-driven fabric that understands and automatically implements and enforces Commander’s Intent for cyber operations. Consistent with the essential Control Plane/Data Plane model from NIST SP 800-207, as shown, software defined networking provides the means to form abstraction layers in the network to reduce the complexities of managing individual devices and enhance security by interlacing a fabric of only those connections that are authorized per Commander’s Intent which is defined in the Policy Decision Point (PDP) and executed by the Policy Enforcement Point (PEP) –across a government hybrid cloud platform.
Advanced identity services coupled with software-defined networking provides the means to implement granular micro-segmentation at scale and speed and enables an automated network fabric that allows users and devices (abbreviated: users/devices) or operational technology (OT) devices (or “devices without users”) to connect more easily and more securely via the control plane. In the physical world, Commander’s Intent is applied through controlling actions via the orders process, according to each unit’s specific identities and defined capabilities. For cyber operations, the network must also be able to apply policy to users and devices – based on their individual capabilities and assigned missions – with full knowledge of how they are connected to the network, and their allowed functions – automatically, at scale and speed. The decision criteria for individuals to access to data in the DoD is usually based on: (1) identification and authentication—does the individual have the proper credentials for identification? and (2) authorization – is the individual authorized to access the data, or “do they have the need to know?”
Advanced identity services continuously incorporates and updates as much contextual information about the status of users/devices, their authorized roles and validated credentials, and their means of access to the network. An intent-driven cyber platform uses this approach for the identity of all OT devices and users/devices that attempt to connect to the network. This challenge/authentication process is not a single event; rather, using dynamic context and identity authentication, the cyber platform, applies least privilege access principles by continuously challenging and authenticating every user/device every time a data access decision must be made – automatically, at machine speed. Thus, Commander’s Intent for the network is applied through network policy controlling actions, via the software defined control plane, according to each user/devices’ specific identities and defined capabilities. These policies are applied before network connection/access is granted with full knowledge of how they are connected to the network, their compliance, their capability status, their allowed functions, and as much contextual information as possible.
Just as important, but especially so in the hybrid cloud environment, Commander’s Intent based controlling actions must be applied and enforced to every application workload across the edge, datacenter, and especially for connections between containers or hypervisors across the hybrid cloud. Application data flow in today’s modern networks flow across an expansive hybrid cloud environment and number in the millions of flows per second. Users and devices must be able to access data and workloads beyond their local environments—including those that are delivered from internet-delivered hybrid cloud services. A software defined networking approach allows for the implementation of a Software Defined Perimeter (SDP) aligned with zero trust philosophy by maintaining a default-deny posture for every transaction. Combined with a profound understanding of the identity of users/devices on the network, an intent-driven cyber platform automatically maps out device workloads and implements application whitelisting across all environments and over millions of flows per second. This SDP-approach creates a protective barrier around high value enterprise applications and data that protects the hybrid environment against emerging cyber threats by dynamically blocking them and only allowing access for registered devices with properly authenticated users.
As part of their digital transformation journey, organizations across the Federal Government are publishing their mission strategies to appropriately leverage cloud-delivered technologies where cloud-delivered capabilities make the most sense. To meet digital transformation needs, it is not a question of whether expanding the consumption of hybrid cloud solutions will be necessary, it is a question of how to best integrate the right capabilities in the most optimal way to support mission outcomes. Software defined networking and advanced identity services provide the means for a government cyber platform to seamlessly adopt these services in the hybrid cloud environment via a zero trust philosophy. The hybrid cloud-enabled cyber platform brings together infrastructure, security, management, open APIs, containers, and tools to create a consistent and secure environment across on-premises data centers and across multi cloud environments.
Transformation. Implementing a Commander’s Intent-driven cyber platform is a necessity for any organization’s digital transformation efforts. Such a cyber platform enables cyber operations at machine speed to empower decision makers with data-driven insights across all of the federal government’s agencies and missions. The close integration of the essential technologies in (1) advanced identity services, (2) software defined networking, and (3) hybrid cloud capabilities enable a government cyber platform to understand and execute Commander’s Intent at machine speed. Implementing these capabilities across edge, data center, and hybrid cloud environments, will provide the government with a platform that provides the means of maneuver for data and, thus, endows a “common foundation of shared data, reusable tools, frameworks and standards, and cloud and edge services” and win the day with decision advantage for the Nation.
The Cipher Brief hosts private briefings with the world’s most experienced national and global security experts. Become a member today.
Read more expert-driven national security insights, perspective and analysis in The Cipher Brief